DevSecOps: Integrating Security into DevOps
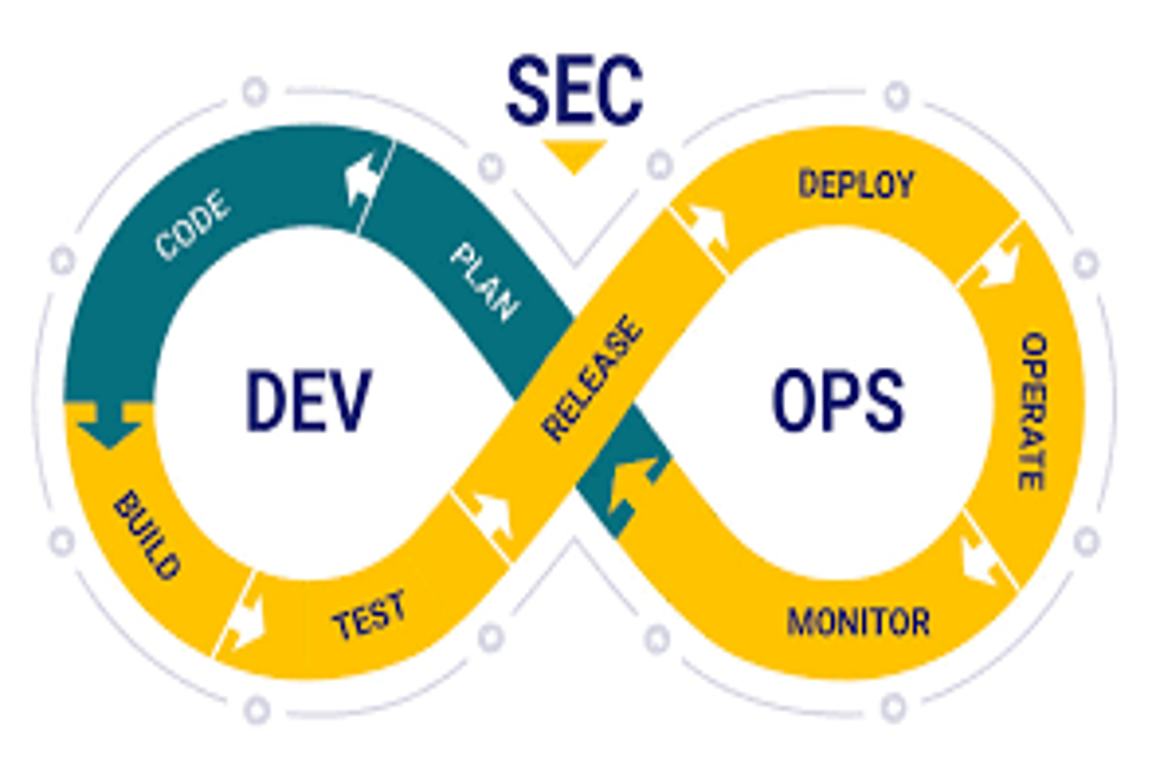
Author: Charu RajputDate: 6 March 2026 Introduction Modern software development moves very fast with DevOps practices such as Continuous Integration (CI) and Continuous Deployment (CD). While speed improves productivity, it can also introduce security risks if security checks are ignored. This is where DevSecOps comes in. DevSecOps means integrating security into every stage of the […]

.webp)
 “APIs have become the backbone of modern applications, handling everything from user authentication to payment processing. Yet these same interfaces represent the largest attack surface for cybercriminals—OWASP data shows API-related breaches jumped 681% in 2024 alone. Unlike traditional web security, API vulnerabilities hide in business logic, authentication flows, and data exposure patterns that standard scanners miss.
“APIs have become the backbone of modern applications, handling everything from user authentication to payment processing. Yet these same interfaces represent the largest attack surface for cybercriminals—OWASP data shows API-related breaches jumped 681% in 2024 alone. Unlike traditional web security, API vulnerabilities hide in business logic, authentication flows, and data exposure patterns that standard scanners miss.


